Qualified Counterintelligence Threat Analyst (Q|CTA)

Qualified Counterintelligence Threat Analyst (Q|CTA)
Trusted by U.S. Military, Law Enforcement, and Government Agencies
Institutionally Approved.
Nationally Recognized.
Government Accepted.
McAfee Institute's certifications are approved, accepted, or recognized by federal, state, and military agencies across the United States.
This includes the Department of Defense (DoD), Police Officer Standards & Training (POST), every branch of the U.S. Military, and the Missouri Department of Higher Education & Workforce Development.
The logos below represent organizations that have formally approved, accepted, or recognized McAfee Institute programs for use in certification, credentialing, or professional development pathways.
Certificate Earned
Qualified Certificate of Completion and 40 CPE Credits
Duration
40 hours of structured video tutorials, interactive quizzes, practical labs, and applied research assignments.
Delivery
Fully online, self-paced learning—accessible anytime, anywhere, designed for flexibility in any schedule.
Guarantee
3-Day Money-Back Guarantee and Lifetime Access—try the course risk-free and view up to 5% of the course, and enjoy lifetime updates.
Program Overview
Eligibility Requirements
McAfee Institute is ranked No. 1 among all training and certification providers for intelligence and investigation education, according to NICCS.
Program Topics
Exam & Renewal Details
Top organizations offer this certification to their employees.
This certification was selected for our collection of top-rated credentials, trusted by government, military, and law enforcement agencies worldwide for its rigor, relevance, and practical application. Backed by recognized standards and comprehensive support, it empowers professionals to excel and drive impactful results.

A Dynamic Learning Environment Built for Your Success
Engage in hands-on, real-world learning through our platform’s intuitive design, built for easy navigation and optimized for lifelong learning. Our user-friendly platform offers everything you need to master critical skills—from in-depth course materials and live instructor support to self-paced quizzes and lifetime access.
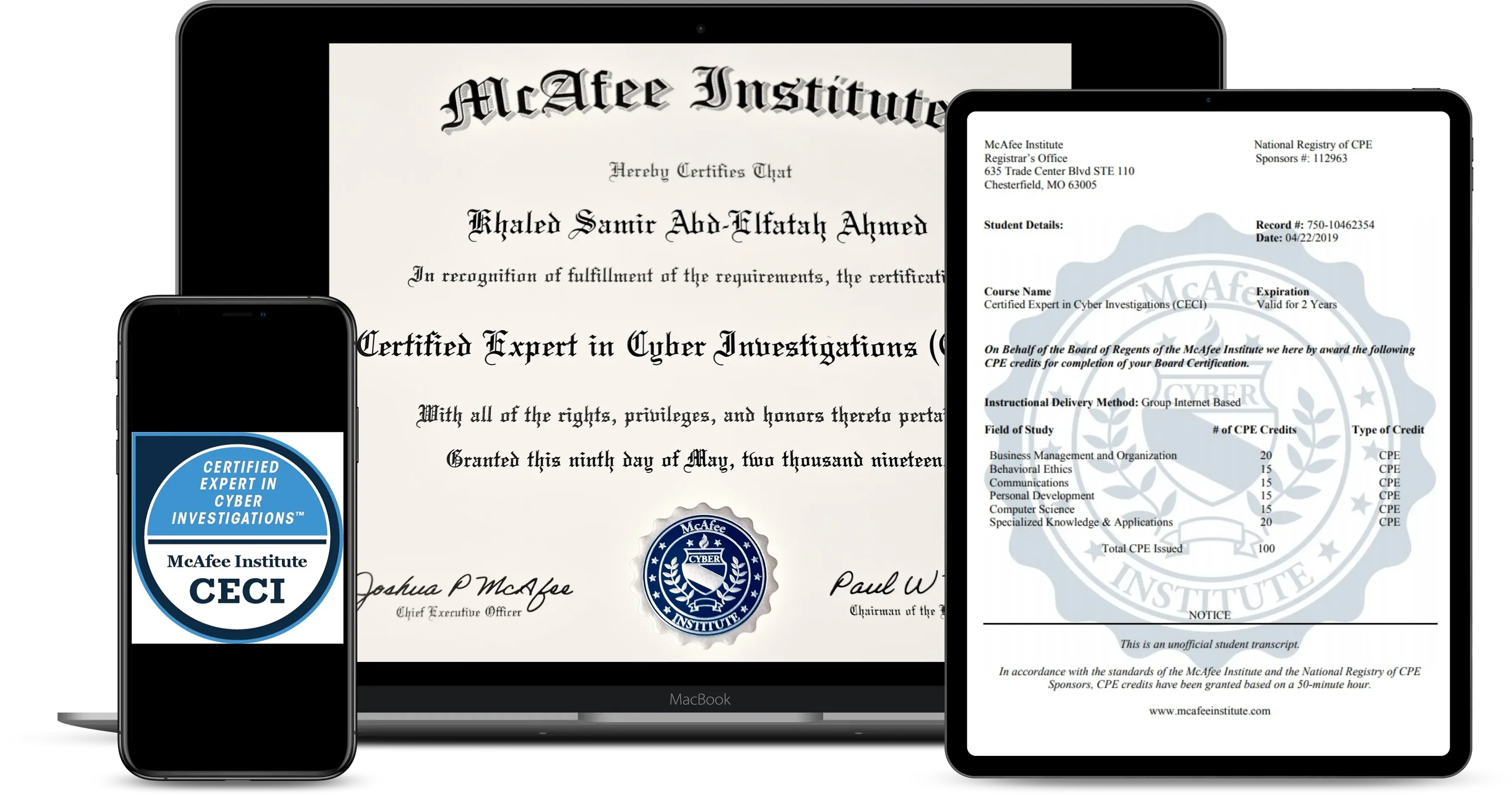
Your Path to a Respected Professional Designation
Gain a powerful credential recognized by top organizations and agencies. Your digital and physical certification reflects the highest standards of excellence in intelligence, investigations, and law enforcement. Your official designation is more than a certification—it's a testament to your commitment and expertise, respected by leaders in law enforcement, intelligence, and beyond.
If you have any questions, you are always welcome to contact us. We'll get back to you as soon as possible, within 24 hours on weekdays.
-
Shipping Information
Use this text to answer questions in as much detail as possible for your customers.
-
Customer Support
Use this text to answer questions in as much detail as possible for your customers.
-
FAQ’s
Use this text to answer questions in as much detail as possible for your customers.
-
Contact Us
Use this text to answer questions in as much detail as possible for your customers.
FAQs
Please read our FAQs page to find out more.
The Program Overview at McAfee Institute
How do I know if this program is right for me?
If you’re considering a McAfee Institute program and want to know if it aligns with your career goals, start by reviewing the detailed information on the program landing page. To dive deeper, submit the quick form at the top of the page to receive a program brochure with more comprehensive insights. If you still have questions or need personalized guidance, reach out to our admissions team at support@mcafeeinstitute.com, and a dedicated program advisor will get in touch with you promptly.
Are there any prerequisites or eligbility requirements for this program?
Certain McAfee Institute programs, particularly the advanced and technical ones, have prerequisites to ensure participants are prepared for the course material. These prerequisites will be listed on the program landing page and are also outlined in the program brochure. If you’re unsure about your qualifications, please email us at support@mcafeeinstitute.com for more details.
Please note: All programs are conducted in English, so proficiency in English is required for successful completion unless otherwise stated.
What is the typical class profile?
McAfee Institute programs attract a highly diverse cohort, both geographically and professionally. Over 50% of participants come from international backgrounds, and our online certificates cater to individuals from a broad range of industries and experience levels. This diversity creates a rich learning environment, offering opportunities for peer learning and networking with professionals across intelligence, investigations, and law enforcement fields.
What other dates will this program be offered in the future?
For the latest information on upcoming program dates and timelines, please check back on this page or email support@mcafeeinstitute.com to inquire about confirmed dates for future program offerings.
What's Included in Your Qualified Program?
Yes, you will not need any other resources or materials as the training program is all inclusive of the content you need to study and pass for the board exam. The only thing additional is if you wish to sit for the board exam which is $450 USD as its NOT included.
What to Expect in the McAfee Institute Learning Experience
How much time is required each week?
Each McAfee Institute program includes a recommended weekly study time to help you balance learning with other commitments. This estimated learner effort is outlined at the top of each program landing page in the “Duration” section. For additional details, you can access our comprehensive program brochure by submitting the quick form available at the top of this page.
How will my time be spent?
We’ve structured our programs to fit seamlessly into your schedule while maximizing the learning experience. Your time will be divided among a range of engaging activities, including:
- Viewing recorded video lectures led by expert instructors
- Reviewing case studies, reading assignments, and interactive examples of core concepts
- Completing prep quizzes and practical exercises to reinforce key skills
- Participating in moderated discussion groups with fellow students
- Complete the final board exam which is online and proctored.
The programs are designed to be interactive, allowing for both guided learning and self-paced reflection. Through diverse activities, you’ll gain a comprehensive understanding of each topic. For questions on specific activities, please feel free to contact us directly.
What is it like to learn online with McAfee Institute?
McAfee Institute’s online programs are trusted by over 4,500 employers and recognized by multiple government and educational bodies. Our programs provide lifetime access to materials, regular updates, and are designed to help you advance your career with confidence. All course materials are made available at the program’s start, with guidance on pacing to ensure learning objectives are met effectively.
Additionally, our dedicated support team is available 24/5 (Monday to Friday) to assist with questions about the learning platform, technical issues, or any other concerns that may arise.
How do I interact with other program participants?
Collaboration and peer learning are key components of the McAfee Institute experience. Our online platform allows you to connect with other professionals, participate in discussion groups, and share insights. This network of peers will enhance your learning and offer valuable connections within the fields of intelligence, investigations, and law enforcement.
Eligibility and Requirements
Eligibility Requirements.
There are no eligibiltiy requirements to attend the training.
What are the requirements to earn the certificate?
Each McAfee Institute program specifies a recommended weekly time commitment so you can evaluate what will be required before enrolling. This information is available at the top of the program landing page under the “Duration” section, as well as in the program brochure, which you can obtain by submitting the short form on this page. Programs are designed to integrate smoothly into your existing schedule.
Each program is assessed on a pass/fail basis. To earn your certification, you must complete all required activities, which may include quizzes, assignments, discussions and a final board exam. Specific requirements are detailed in the program brochure. If you have questions about particular requirements, feel free to reach out to us for clarification.
What type of certificate will I receive?
Upon successful completion, you’ll receive a verified digital certification from McAfee Institute. This digital certification can be shared with friends, family, employers, or colleagues and can be featured on your cover letter, resume, and LinkedIn profile to showcase your achievement. Your digital certification will be sent approximately 24-48 business hours after program completion.
Can I get a hard copy of the certificate?
Yes, McAfee Institute provides a verified digital certificate upon successful completion of the program. The digital version allows easy sharing on platforms such as LinkedIn.
Do I receive alumni status after completing this program?
Yes formal alumni status is conferred upon program completion. All programs provide CPE credits that count toward other certifications. Information on these credits, if available, will be included in the program brochure.
How long will I have access to the learning materials?
McAfee Institute provides lifetime access to your program materials. This includes all videos, resources, and updates to the course content, ensuring that you can revisit and stay current with the latest knowledge and practices in your field.
Payment Options and Process at McAfee Institute
What is the program fee, and what forms of payment do you accept?
The program fee is noted at the top of this program web page and usually referenced in the program brochure as well.
- Flexible payment options are available (see details below as well as at the top of this program web page next to FEE).
- Tuition assistance is available for participants who qualify. Please email admissions@mcafeeinstitute.com
What if I don’t have a credit card? Is there another method of payment accepted?
Yes, you can do the bank remittance in the program currency via wire transfer or debit card. Please contact your program advisor, or email us for details.
I was not able to use the discount code provided. Can you help?
Yes! Please email us with the details of the program you are interested in, and we will assist you. Discount cannot be used in combination of other promtions, scholarship offers or reduced tuition.
How can I obtain an invoice for payment?
Please email us your invoicing requirements and the specific program you’re interested in enrolling in.
Is there an option to make flexible payments for this program?
Yes, the flexible payment option allows a participant to pay the program fee in installments. This option is made available on the payment page and should be selected before submitting the payment.
How can I obtain a W9 form?
Please connect with us via email for assistance.
Who will be collecting the payment for the program?
McAfee Institute collects all program payments, provides learner enrollment and program support, and manages learning platform services.
Refund Policy for McAfee Institute Programs
What is the program refund and policy?
We offer a NO-Questions-asked 3 day money-back guarantee from the date you enroll in your program, you can view up to 5% of the program. If you are not satisfied with your program for any reason please let us know. https://www.mcafeeinstitute.com/policies/refund-policy
Proctored Exams: Does McAfee Institute Require One?
The McAfee Institute utilizes ProctorU which is an online exam proctoring services for all courses which require a proctored exam. This secure, cloud-based proctoring service allows students to take secure exams at their convenience while maintaining university integrity. The exam can be accessed through www.mcafeeinstitute.com. More instructions and training videos for utilizing ProctorU can be viewed in the New Student Orientation.
How Do Scholarship Opportunities at McAfee Institute Work?
OVERVIEW
You cannot combine discount codes or other promotional offers on scholarship offers. Discount codes are valid on full price items only and cannot be combined. Scholarships are applied directly to the price of the enrollment tuition. No other codes are needed.
FINANCIAL NEED
Scholarships are available to students in financial need. They are not for employer or military purchases. Scholarships are based on sponsors and thier needs as they are sponsoring a students enrollment. Scholarships are limited and not always available.
AVAILABILITY
Scholarships are limited in the number we offer and the amount. Once they are gone they are gone. If a scholarship is available it will be listed on the course page and applied to the price on the website.
HOW TO SECURE A SCHOLARSHIP
It is easy to secure your scholarship. Simply enroll in the program of choice when a scholarship is available.
ELIGIBLITY
Scholarships are designed for students in finacial need only. McAfee Institute reserves the right to verify and validate financial need of the student on enrollment into the program.
MILITARY FUNDING
Please note that scholarship pricing offered through McAfee Institute is not applicable to military funding programs, including but not limited to Credentialing Assistance (CA), COOL or other military tuition assistance programs. Military personnel utilizing these funding sources will be subject to the standard program pricing as outlined in the respective funding guidelines.
Certification Renewal: Requirements and Steps
What is the renewal process for my certification?
To maintain your McAfee Institute certification, renewals are required every two years. The renewal process includes:
- Cost: The renewal fee is $125, which extends your certification for an additional two years.
- Continuing Education: You must provide proof of completion for a certain number of Continuing Professional Education (CPE) credits. This ensures that your skills remain sharp and up-to-date with industry standards. you can find those requirements here.
For additional details or assistance with the renewal process, please contact our support team at support@mcafeeinstitute.com.
System Requirements for McAfee Institute Programs
You cannot use a VPN, TVN or Proxy to access our site our course materials due to our security measures. In addition you will need a laptop or desktop computer as well. Review the following requirements for your camera, operating system, upload/download speeds, RAM, ports, microphones, and browsers. Also included is a list of technology not currently supported by ProctorU.
Recomended
Internet Connection
Wifi Connection
Wired Connection
PC Users
Windows 10 (Windows 10 S mode is not supported)
Windows 11
Mac Users
MacOS 10.13 (Oldest Still Maintained Version)
MacOS 10.15
CPU
More than 2 core CPU, less than 85% CPU Usage
More than 4 core CPU, less than 50% CPU Usage
Webcam
640x480 resolution
1280x720 resolution
Internet Download Speed
1 Mbps
12 Mbps
Internet Upload Speed
1 Mbps
3 Mbps
RAM
4 GB, less than 95% Ram Usage
16 GB, less than 90% Usage
Connectivity Ports
1935, 843, 80, 443, 61613, UDP/TCP
1935, 843, 80, 443, 61613, UDP/TCP
Screen Resolution
1366 x 768
1920 x 1080 and above
Additional Requirements:
- A functioning microphone (some web cameras have them built-in); microphone should not be part of headphones
- Headphones are generally not permitted, check with your testing organization to determine if headphones are permitted
- A compatible browser: Google Chrome (preferred) or Mozilla Firefox
Not Supported:
- Microsoft Edge browser
- Google Chromebooks (with Guardian Browser)
- Google Chromebooks for Live+ or Review+
- Tablets (Nexus, iPad, Tab, Note, etc.)
- Smartphones
- Linux operating systems
- Windows 10 in S mode or Surface RT
- Connecting from within a virtual machine. You will be asked to reconnect using your host operating system to take your exam
Use of VPNs, Virtual Machines, and Proxies During the Course & Exam
You cannot use a VPN, TVN or Proxy to access our site our course materials due to our security measures.
Sensitive Content Disclaimer: What You Should Know
Disclaimer: Exposure to Sensitive ContentPlease be aware that the programs and certifications offered by the McAfee Institute may include content that some participants might find disturbing or offensive. By enrolling in our courses, you acknowledge that you may be exposed to materials that include, but are not limited to, adult language, nudity, graphic depictions of death, explicit discussions of political issues, scenes depicting intense violence, and real-world criminal scenarios. Additional sensitive topics may include racial and ethnic tensions, sexual content, religious contexts, mental health issues, substance abuse, terrorism, child abuse and exploitation, as well as corruption and extreme ideologies.
Context and Humor in Training:Our training sometimes incorporates humor to facilitate learning and engagement. Please understand that any humor used is intended to enhance the educational experience and is not meant to be offensive or belittle serious topics. Furthermore, discussions in our courses may cover sensitive topics such as nudity and death as they are relevant to law enforcement scenarios. Political discussions and analyses of various countries and cultures are also integral to our training, aimed at providing a comprehensive understanding of global and domestic issues as they relate to law enforcement.
Intent and Educational Purpose:These elements are included for educational purposes and are intended to provide a realistic view of the subjects under study. Our aim is not to offend or cause distress but to prepare you for real-life situations you may encounter in your professional life. We strive to handle all content with the utmost respect and professionalism, keeping in mind the diverse backgrounds of our participants.
Participants are advised to consider their personal sensitivities and circumstances before enrolling. If at any time you feel uncomfortable, we encourage you to reach out to an instructor or program coordinator for support and guidance.
By continuing with the enrollment and participating in the courses, you explicitly agree and understand that the McAfee Institute is not liable for any emotional distress, discomfort, or offense that may arise from exposure to such content or the manner in which it is presented. This includes understanding that certain topics may evoke strong emotional responses due to personal experiences or beliefs, and participants are expected to manage their engagement according to their own discretion and advice from medical or psychological professionals if necessary.
Your decision to proceed with the course indicates your acceptance of this potential exposure and an acknowledgment of the educational purpose behind including such content in our curriculum.
Flexible Financing Options for Your Certification
We offer several options to help you afford tuition for the Professional Certification in OSINT.
Available opportunities to lower tuition fees include:
Referrals – You and a colleague can each receive $695 off your tuition when you enroll together. Refer now
Group enrollments – A discount of up to 20% is available for group enrollments. For more information, email. admissions@mcafeeinstitute.com.
US Residents
Sezzle*
Fixed repayment, interest-only repayment, and deferred payment options available. Click here to learn more
Shop (Affirm)*
Fixed repayment, interest-only repayment, and deferred payment options available. Click here to learn more
Climb Credit
Immediate repayment, interest-only repayment, and deferred payment options available. Click here to know more
Flexible Payment Options For All
Flexible Payment Options – Monthly payments as low as US$1,494. Choose to pay in two, three, or six monthly installments for higher flexibility Click here to learn more
Is McAfee Institute accredited?
McAfee Institute is certified by the Missouri Department of Higher Education & Workforce Development (MDHEWD) to operate as a proprietary school in the state of Missouri.In addition, our certification programs are formally approved or recognized by national and state agencies, including:
- Department of Defense (DoD)through the Credentialing Assistance (CA) and COOL programs
- National Initiative for Cybersecurity Careers and Studies (NICCS)
- Police Officer Standards and Training (POST)in multiple states
These recognitions support the use of our programs for credentialing, professional development, continuing education, and tuition assistance across the government, military, and private sectors.
Note: McAfee Institute is not currently institutionally accredited by a U.S. Department of Education-recognized accrediting agency.